Smart IT Hub 211597820 implements a multifaceted security framework aimed at protecting sensitive information. Through robust user authentication and strict access controls, it effectively limits data exposure. Advanced encryption algorithms further fortify its defenses against unauthorized access. Continuous monitoring and proactive threat detection are also integral to its strategy. However, the question remains: how do these measures translate into practical benefits for users, and what role can they play in enhancing their own security practices?
Understanding Smart IT Hub 211597820’s Security Features
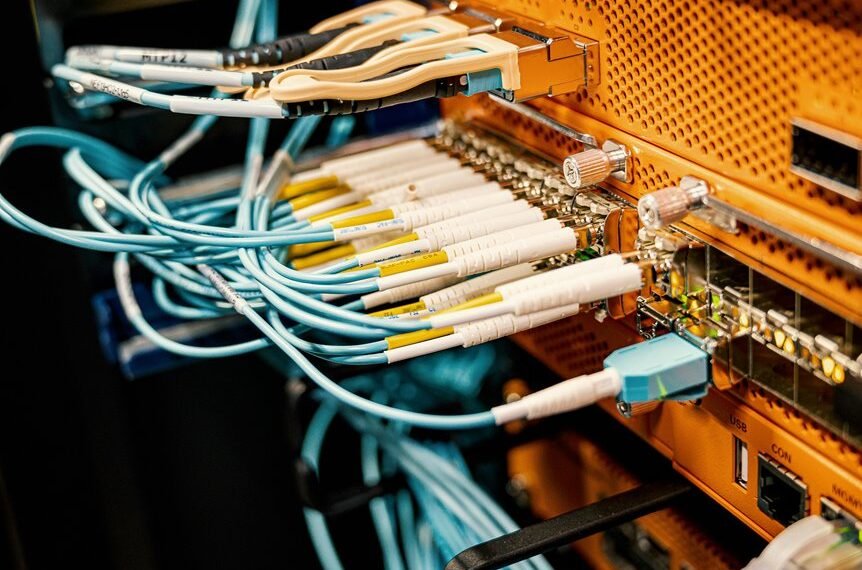
The security architecture of Smart IT Hub 211597820 is designed to mitigate risks and protect sensitive data effectively.
Central to this framework are robust user authentication methods and stringent security protocols. These mechanisms ensure that only authorized users gain access, thereby safeguarding personal information.
How Does Smart IT Hub Protect Your Data From Cyber Threats?
How effectively does Smart IT Hub combat cyber threats to ensure data integrity? Through advanced threat detection mechanisms and proactive monitoring, it safeguards data privacy.
The Role of Encryption in Smart IT Hub Security
Encryption serves as a fundamental pillar of Smart IT Hub’s security framework, ensuring that sensitive data remains inaccessible to unauthorized users.
By employing robust encryption algorithms, the hub fortifies data privacy, safeguarding against potential breaches.
This proactive approach not only enhances user trust but also emphasizes the importance of protecting personal information in an increasingly interconnected digital landscape, fostering a secure environment for all users.
Best Practices for Users to Enhance Security on Smart IT Hub
Robust encryption measures lay the groundwork for safeguarding data, but users also play a pivotal role in enhancing security on the Smart IT Hub.
Implementing strong user authentication protocols and stringent access control policies significantly reduces vulnerabilities.
Regular updates and vigilance against phishing attempts further empower users, fostering an environment of proactive security awareness that champions freedom while protecting sensitive information from unauthorized access.
Conclusion
In a world where data breaches are as common as morning coffee, Smart IT Hub 211597820 stands as a fortress, ironically shielding users from threats they may not even know exist. With its robust security features and proactive measures, it ensures that the very information users often overlook remains protected. Thus, while individuals may underestimate the importance of security, the hub’s comprehensive framework serves as a stark reminder that vigilance, even in the digital realm, is paramount.