Advanced IT Hub 963008707 Security presents a sophisticated framework designed to protect sensitive information through advanced encryption and real-time threat detection. Its proactive measures ensure immediate response to potential breaches, preserving operational integrity. With compliance to regulatory standards and regular risk assessments, the hub addresses the challenges posed by evolving cyber threats. However, understanding the full scope of its capabilities and implications on organizational resilience prompts further exploration into its strategic implementations.
Key Features of Advanced IT Hub 963008707 Security
The security framework of Advanced IT Hub 963008707 incorporates several critical features designed to safeguard sensitive data and mitigate potential threats.
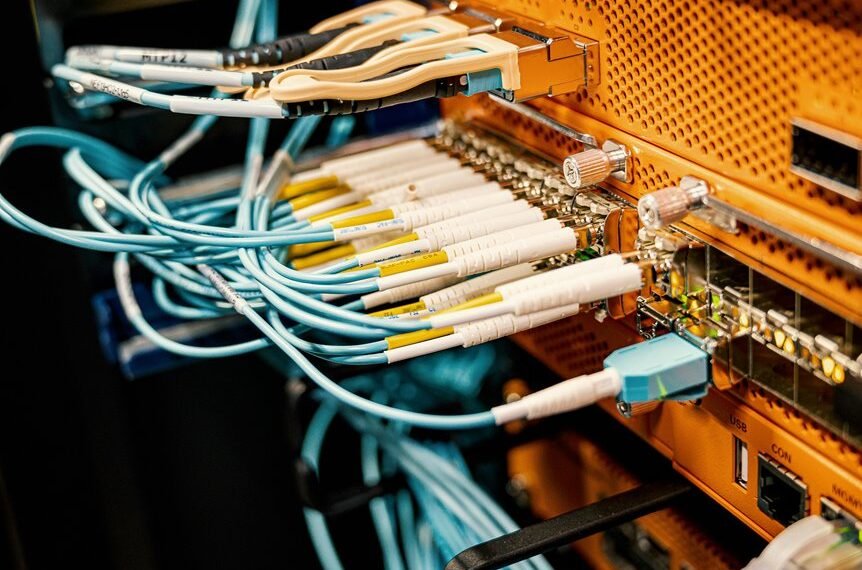
Network encryption ensures that data remains confidential during transmission, while advanced threat detection systems continuously monitor for anomalies, enabling proactive responses to potential breaches.
These features collectively enhance the security posture, empowering users to operate freely without compromising their data integrity.
How Does Advanced IT Hub 963008707 Security Mitigate Cyber Risks?
While organizations increasingly face sophisticated cyber threats, Advanced IT Hub 963008707 implements a robust security architecture to effectively mitigate these risks.
The integration of advanced threat detection mechanisms allows for real-time monitoring and rapid response. Coupled with thorough risk assessment protocols, potential vulnerabilities are identified and addressed proactively, ensuring that organizations can maintain operational integrity and protect sensitive data against evolving cyber threats.
Benefits of Implementing Advanced IT Hub 963008707 Security Solutions
Implementing Advanced IT Hub 963008707 security solutions yields numerous advantages that enhance organizational resilience against cyber threats.
These solutions not only facilitate cost savings through streamlined operations but also ensure compliance assurance with regulatory standards.
Best Practices for Maximizing Your Security With Advanced IT Hub 963008707
Maximizing security with Advanced IT Hub 963008707 requires a strategic approach that encompasses a variety of best practices tailored to the specific needs of the organization.
Implementing robust security protocols is essential, alongside regular risk assessments to identify vulnerabilities.
Organizations should prioritize staff training, data encryption, and continuous monitoring to ensure an adaptive security posture that evolves with emerging threats and promotes operational freedom.
Conclusion
In a landscape where data breaches are the norm, Advanced IT Hub 963008707 Security emerges as a beacon of hope—one might say a fortress in a world of paper walls. With its robust encryption and real-time threat detection, it ironically highlights the fragility of conventional security measures. As organizations cling to outdated strategies, the hub’s proactive approach underscores a critical truth: in cybersecurity, the only constant is change, demanding vigilance and adaptation to outpace relentless threats.